Evaluate your organization's cybersecurity posture against the industry-standard CIS Critical Security Controls framework.

The CIS Critical Security Controls are a prioritized set of actions developed by the Center for Internet Security that collectively form a defense-in-depth set of best practices to mitigate the most common cyber attacks.
Organized into 18 critical security control areas covering everything from inventory management to incident response and penetration testing.
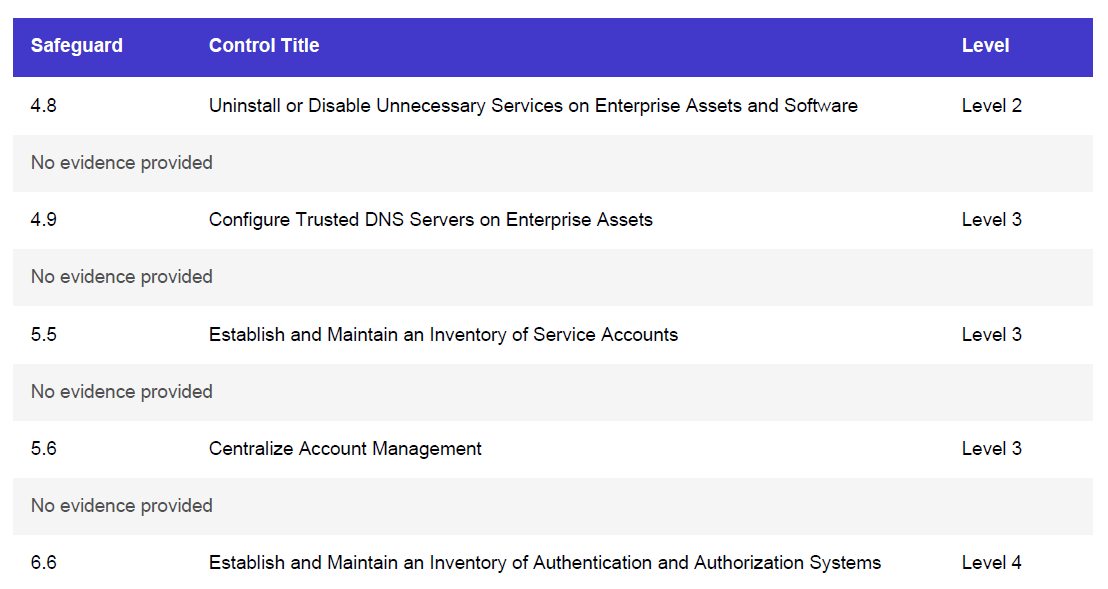
Each control contains specific safeguards — actionable security measures that can be implemented and measured within your organization.
Controls are prioritized based on real-world attack data, focusing your efforts on the actions that provide the greatest security benefit.
CIS Controls are organized into three Implementation Groups based on organizational size, resources, and risk profile. This helps you prioritize which safeguards to implement first.
The foundational set of cyber defense safeguards that every organization should implement. Designed for small organizations with limited IT resources.
Additional safeguards for organizations with moderate resources that handle sensitive data and face more sophisticated threats.
The complete set of safeguards for organizations with significant security resources that must protect highly sensitive data.
From small businesses to large enterprises looking to establish or improve their security baseline.
CIS Controls map to many regulatory frameworks including NIST, ISO 27001, PCI-DSS, and HIPAA.
The prioritized approach helps you focus limited resources on the most impactful security controls.
Track your security maturity over time and demonstrate progress to leadership and stakeholders.
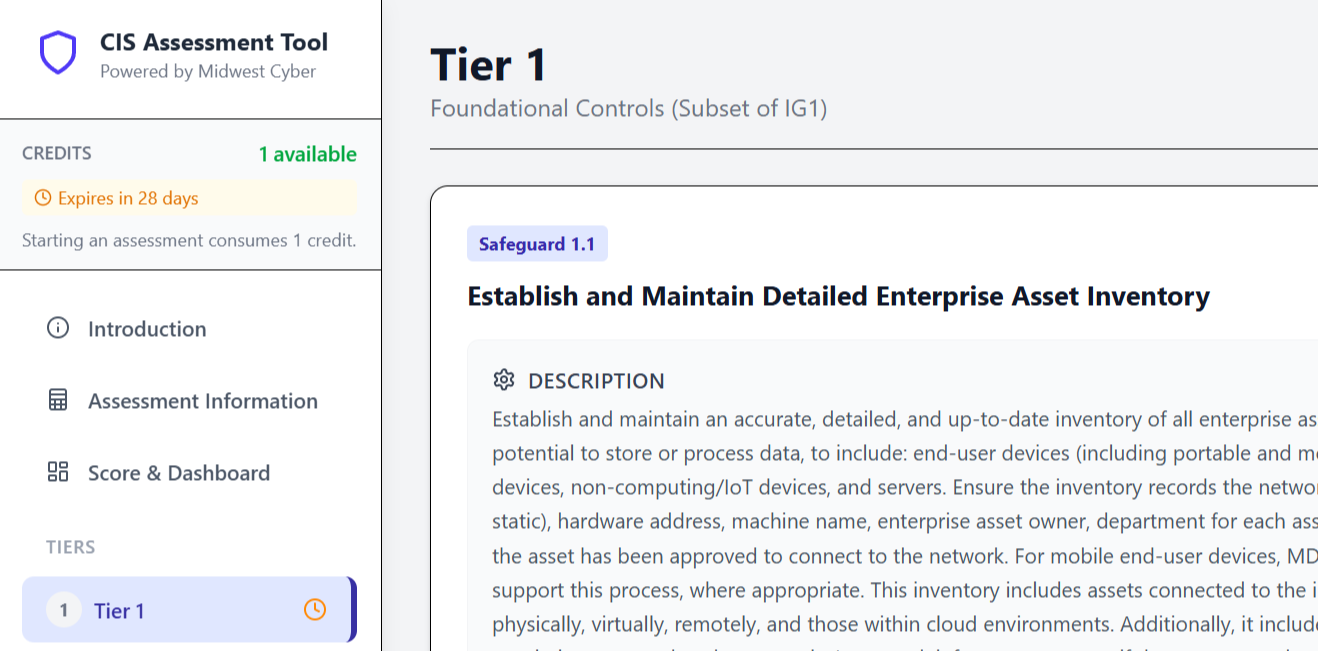
Our assessment tool guides you through all 153 safeguards with a simple, intuitive interface. Save your progress and return anytime.
Navigate through 10 progressive tiers, each building on the security foundations of the previous tier.
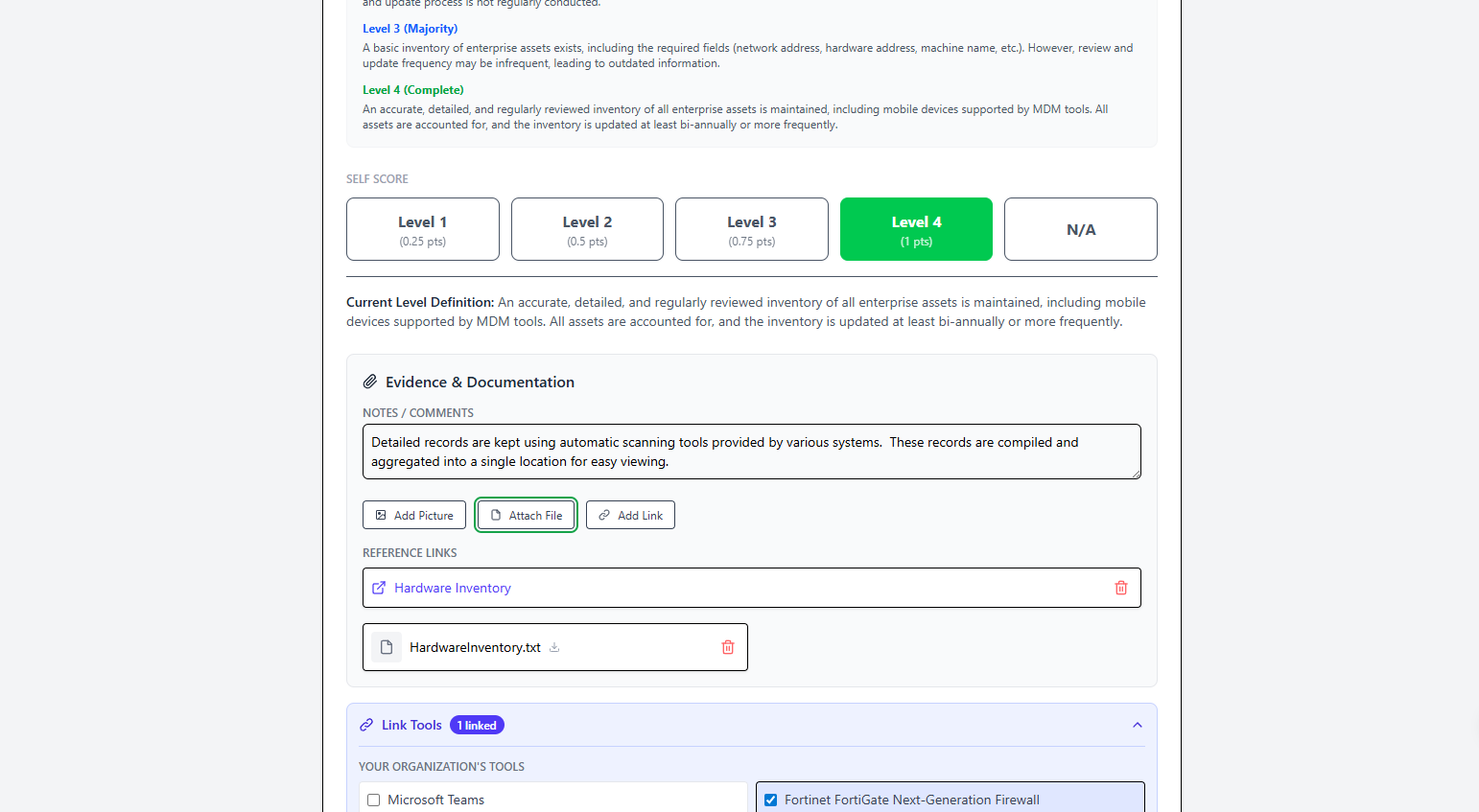
For each safeguard, indicate your implementation level: Not Implemented, Partially, Mostly, or Fully Implemented.
Document your implementation details, responsible parties, and any evidence for each safeguard.
Once complete, generate professional PDF reports and secure backups of your assessment data.
A complete assessment typically takes 2-4 hours, depending on your organization's complexity and how thoroughly you document each safeguard.
Upon completing your assessment, you'll have access to comprehensive reports that help you understand your security posture and plan improvements.
A high-level overview designed for leadership and stakeholders. Includes overall maturity scores, Implementation Group progress, and visual charts showing your security posture at a glance.
A comprehensive report listing every safeguard with your implementation rating, notes, and evidence. Perfect for technical teams and audit documentation.
A password-protected JSON file containing all your assessment data. Use it to restore your assessment on any device or transfer between accounts.
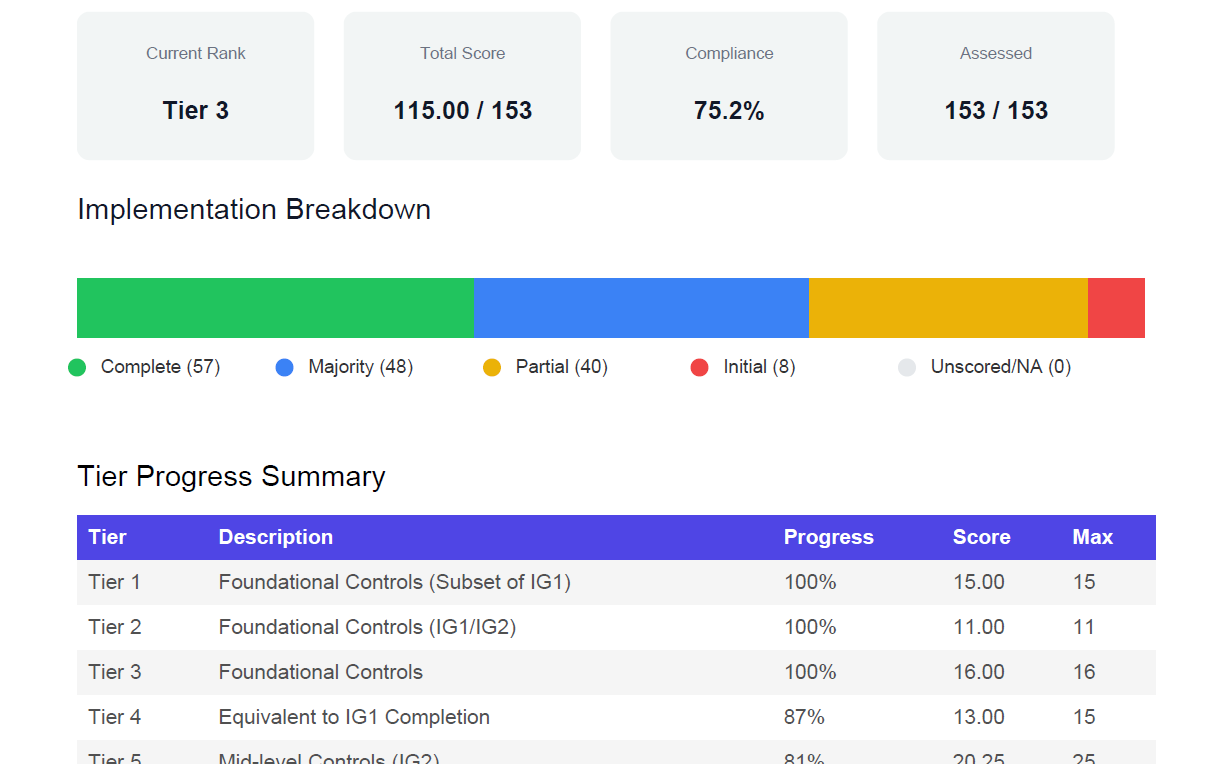
Beyond your core deliverables, every CIS Controls assessment unlocks a full suite of analytics, AI-powered reports, and remediation planning tools through the Analysis Dashboard.
Communicate findings to executives, boards, and auditors with presentation-ready reports.
Prioritize and track remediation with actionable gap analysis and milestone planning.
Explore your security posture through interactive dashboards and visualizations.
Safeguards are organized into 10 progressive tiers, allowing you to build your security program incrementally. Each tier builds upon the previous, creating a natural implementation roadmap.
Try our CIS Controls assessment tool with a free trial. Create an account to save your progress and generate professional reports.